What is the NPI JSON API on NPIPublicData.org for?
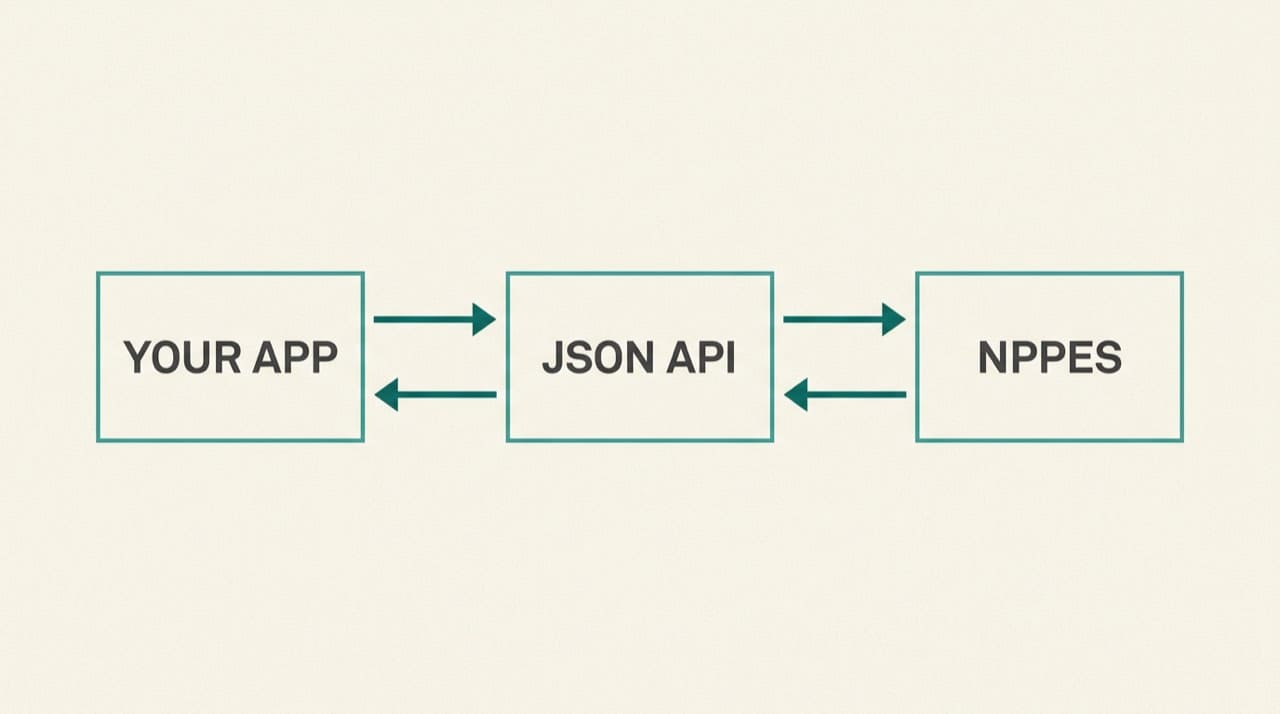
We expose an HTTP JSON API so engineers can validate NPIs, power internal search boxes, and prototype integrations without driving a full browser. It is a convenience layer on this site with our own rate limits, uptime, and response shape. It is not a substitute for reading CMS rules when you are deciding legal enumeration questions, and it is not the same thing as calling CMS systems directly when your compliance checklist forbids intermediaries.
Reconcile high-stakes rows on the NPPES NPI Registry search on whatever cadence risk approves. Program background: CMS NPI overview. Public data and file products: Data Dissemination.
Read the live reference
Complete parameters, auth headers, and examples live in API documentation. This guide is orientation only. Production clients should target the versioned path documented there (for example GET /api/v3/npi) and pin versions until you have tested upgrades.
Secrets, CORS, and server-side calls
Store API keys in a secrets manager. Prefer a small backend proxy over exposing keys in browser bundles unless you accept that risk openly. Even when CORS allows a call, front-end keys leak through devtools and history.
Log request IDs on the server side, not full payloads, unless privacy review approves otherwise. NPIs are identifiers, not passwords, but your logs still deserve minimization.
Rotate keys on the same schedule as other third-party credentials. A leaked key that sits in a public repo for a weekend can burn through quotas before anyone notices the traffic spike.
Rate limits and fair use
Cache where policy allows. For millions of rows, prefer Downloads plus a database over hours of interactive calls. Responsible handling of extracts: using bulk NPI files responsibly.
Teach client teams that 429 responses are a signal to back off, not a cue to spawn more parallel workers.
Batch jobs that loop tens of thousands of NPIs should log progress checkpoints so a mid-run failure does not restart from zero and hammer the gateway twice.
Schema stability and contract tests
Pin a few golden NPIs in automated tests that assert required keys still exist after deploys. When we add fields, your parsers should tolerate unknown properties instead of failing closed on extras.
Document which JSON properties your product surfaces to users versus which stay internal so a schema tweak does not silently rename a column in a dashboard.
Mobile and desktop clients should share the same backend integration layer when possible so you do not maintain two divergent parsers that disagree after a deploy.
Product positioning and compliance language
Marketing copy should not imply that calling our gateway is identical to calling CMS. If your risk team needs independence statements for slide decks, start with About us and adapt with counsel so nothing reads like a government endorsement.
When a customer contract demands “direct CMS verification,” read that clause literally. Our API may still be useful internally, but the signed obligation might require registry screenshots or another approved path.
Monitoring and runbooks
Track latency, error rates, and quota behavior. Alert on deploy-correlated spikes. Keep curl examples and expected success shapes in on-call docs.
Include a short “known good” NPI list in runbooks that spans active and deactivated examples if your product must handle both shapes. That prevents on-call engineers from guessing with random digits during an outage.
When responses look wrong
Capture timestamps, request parameters, and sample NPIs. Contact us for gateway bugs. We cannot edit NPPES through that form. Mirror framing: third-party NPI sites and the official registry.
Before you file a bug, confirm the same NPI on the official registry search UI with the same digit string you sent to the API. Typos and leading-zero mistakes in client code create ghosts that waste everyone’s time.
Official change channels
Enumeration corrections flow through CMS/NPPES, not our API. Routing help: contacting CMS and NPPES for official changes. If staff need lookup coaching before they escalate, send them to how to look up a provider's NPI.
FAQ for product managers
Short non-engineering answers: FAQ. Site scope and liability: Disclaimer.
Practical next steps
Create a dev key, run the documented example against /api/v3/npi, validate fields your app needs, then define caching TTL and CMS reconciliation policy before customer traffic arrives. Schedule a quarterly review of the same live reference page for diffs so version bumps never surprise production on a Friday deploy.