What does responsible use of bulk NPI data mean?
CMS publishes NPPES extracts so the industry can align on stable identifiers, not so every team can spray contact lists into uncontrolled channels. Phone numbers and addresses in bulk files are still real operational endpoints for clinics and suppliers. Treat extracts as infrastructure data with retention limits, access control, honest labeling in products, and counsel-approved marketing boundaries.
Confirm what the public row actually shows using the NPPES NPI Registry search when you train non-technical staff. Identifier program context: CMS NPI overview. Public data products and dissemination framing: Data Dissemination.
Spam, cold outreach, and reputational risk
Harvesting registry contact paths for aggressive dialers invites blocks, complaints, and legal exposure. Prefer opt-in channels your counsel recognizes. Even when a number is public in NPPES, volume and tone still create liability your security team will not enjoy explaining.
Regulatory inquiries sometimes ask how you sourced a list. If the honest answer is “we scraped a mirror last Tuesday,” expect uncomfortable follow-up questions about retention and consent. Build sourcing metadata up front so you are not reconstructing it under pressure.
Vendors and subprocessors
When you share extracts, you remain responsible for encryption, access reviews, and breach playbooks. Put data-processing expectations in writing and review quarterly, not only at contract signature.
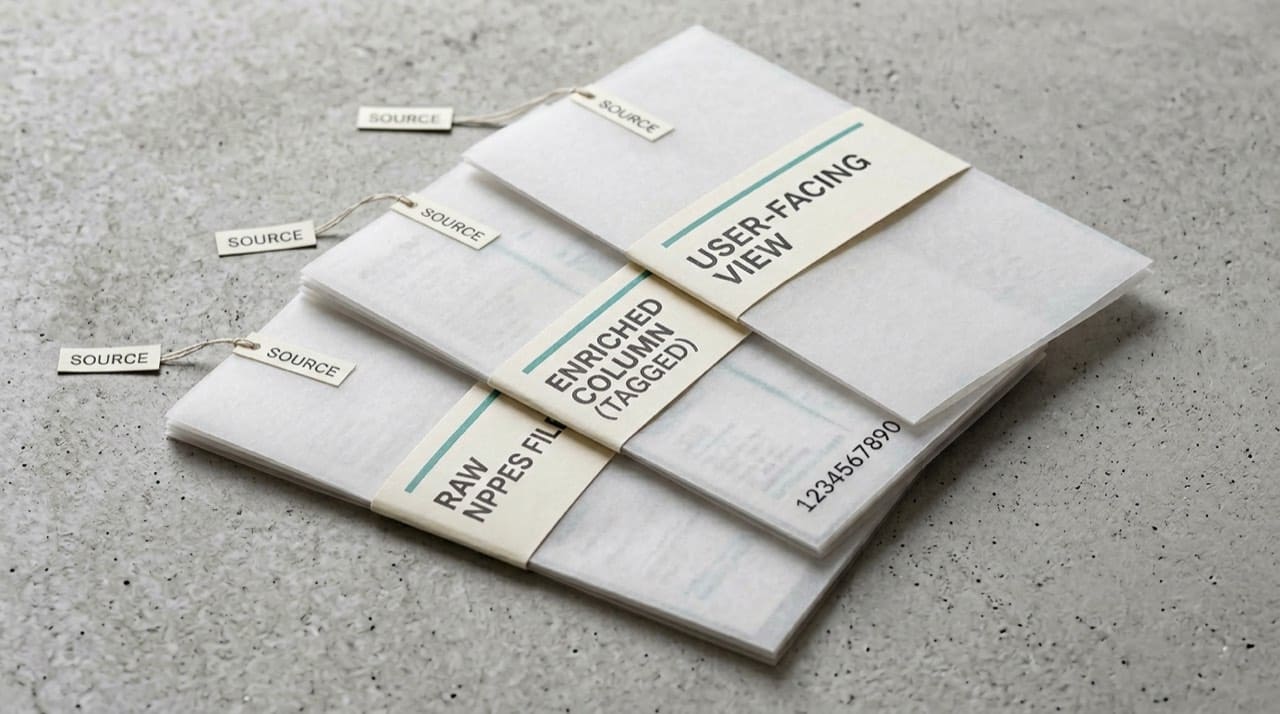
Require vendors to separate CMS columns from proprietary enrichments in their exports back to you. Silent merges turn a defensible government snapshot into an untraceable soup when auditors ask for lineage.
Subprocessor spreadsheets should list every environment where a copy lives, including laptops used for demos. Shadow IT exports are where most “public data” incidents actually start.
Researchers, maps, and small-area risk
Aggregate thoughtfully when small-area geography plus specialty could identify thin-market individuals. Follow IRB or newsroom ethics guidance when unsure.
When publishing charts, prefer rolled-up geographies and rounded counts unless legal has signed off on finer grain.
If you blend NPPES with claims or payroll, treat the combined set as higher sensitivity than either source alone. Access reviews and purpose limitation should tighten automatically when joins add clinical or financial context.
Analyst training and “helpful” exports
New hires love emailing CSV extracts because it feels fast. Build approved export paths with watermarks, expiring links, and DLP rules so “just this once” attachments do not become a culture.
When someone asks whether a column is safe to share externally, point them at third-party NPI sites and the official registry for how mirrors relate to CMS, then escalate anything non-public to counsel.
Operational mistakes in claim and directory systems
Scrubbers and clearinghouses sometimes cache NPI rows longer than your warehouse. Align refresh expectations with partners so a correct NPPES value does not bounce for a week because a vendor’s middle tier is stale.
For how identifiers land on claims versus tax paperwork, see billing, claims, and NPI basics for billers. That guide is not legal advice, but it steers teams away from mixing up roles.
Engineering patterns that scale without bruising mirrors
Use exponential backoff on failed downloads, respect announced maintenance windows, and store immutable raw files before transforms. National backfills belong in a database you control, not in thousands of interactive lookups.
For monthly versus weekly cadence and deactivation handling, read CMS full replacement NPI file overview and weekly NPI files, deactivations, and incrementals as a pair.
Official bulk sources
Downloads orients toward CMS. For programmatic validation at lower volume, NPI JSON API overview for developers explains our JSON surface and its limits.
When data is wrong in the source
We cannot correct NPPES rows from this site. Authorized entities update through CMS channels; orientation lives in contacting CMS and NPPES for official changes. Operational hygiene before you escalate: when to update NPPES and correct NPI data.
Who operates this site
About us clarifies independence from CMS. Display or ethics questions: Contact us. Quick policy reminders for visitors: FAQ. Mirror and liability framing: Disclaimer.
Practical next steps
Write a one-page internal policy: allowed uses, prohibited uses, approver for exceptions. Review databases for columns you no longer need and mask or drop them on a schedule security agrees with. Run a tabletop exercise for mis-sent CSVs at least yearly. Add a data catalog tag on every NPPES-derived column so analysts know which fields are government-sourced versus modeled.
Schedule semiannual refreshers that walk through troubleshooting when an NPI is not found so support teams stop inventing folklore about “missing” numbers that are really typos or filters.
